Island is an app that allows you to isolate, clone, freeze, hide, archive apps.
Unfortunately when you use it with iptables firewall app like AFWall the apps placed in the work profile have no access to the network. (because there aren’t rules allowing them in the firewall)
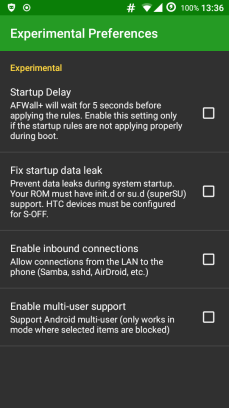
AFWall doesn’t support multiple profiles – there’s an experimental option called “multi-user support" but only works in mode where selected items are blocked:
AFWall doesn’t show work profile apps. So I need a way to allow work profile app traffic.
With a bit of digging, I found the rule for work profile (UNIX) uid : user_id*100000+app_uid , the primary user has user id of 0, the work profile Island created has user id 10.
So you can go look for app uid, add user_id*100000 , and it becomes the (UNIX) uid of the app in that work profile.
A quick way to know app_uid is go to AFWall preferences > User interface > “Show UID for apps".
Then you need to write your own rules that allows traffic to pass through, the number after --uid-owner is the UID you want to change, in this example I allowed 3 apps:
| IP6TABLES=/system/bin/ip6tables | |
| IPTABLES=/system/bin/iptables | |
| $IPTABLES -A afwall-3g-home -m owner --uid-owner 1010082 -j RETURN | |
| $IPTABLES -A afwall-3g-home -m owner --uid-owner 1010105 -j RETURN | |
| $IPTABLES -A afwall-3g-home -m owner --uid-owner 1010172 -j RETURN | |
| $IPTABLES -A afwall-wifi-wan -m owner --uid-owner 1010082 -j RETURN | |
| $IPTABLES -A afwall-wifi-wan -m owner --uid-owner 1010105 -j RETURN | |
| $IPTABLES -A afwall-wifi-wan -m owner --uid-owner 1010172 -j RETURN |
Place it in /data/local/, chmod +x it, add its path to AFWall custom script, then apply rules in AFWall. You should now get internet in work profile apps.